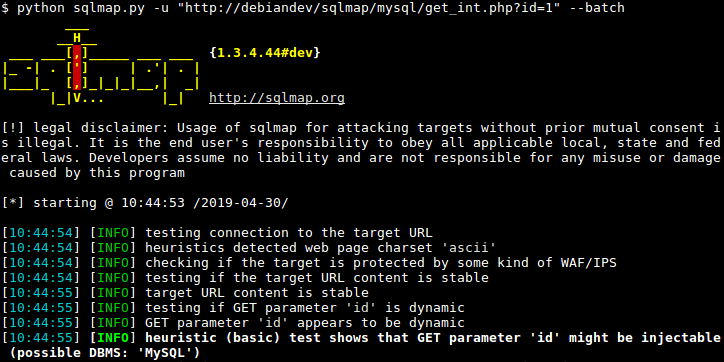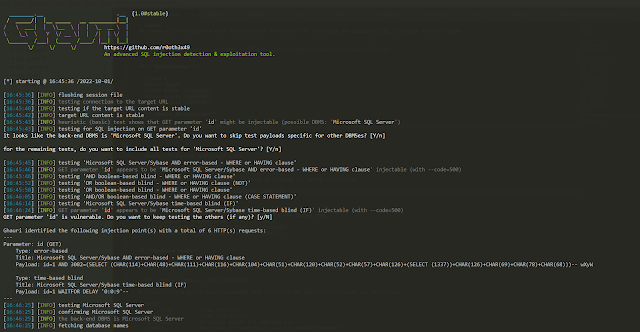
Ghauri - An Advanced Cross-Platform Tool That Automates The Process Of Detecting And Exploiting SQL Injection Security Flaws

Applied Sciences | Free Full-Text | Deep Learning-Based Detection Technology for SQL Injection Research and Implementation
![PDF] Comparing SQL Injection Detection Tools Using Attack Injection: An Experimental Study | Semantic Scholar PDF] Comparing SQL Injection Detection Tools Using Attack Injection: An Experimental Study | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/00d2d85dce5a30b8355051285fb4bd5e8cf92de0/2-Figure1-1.png)
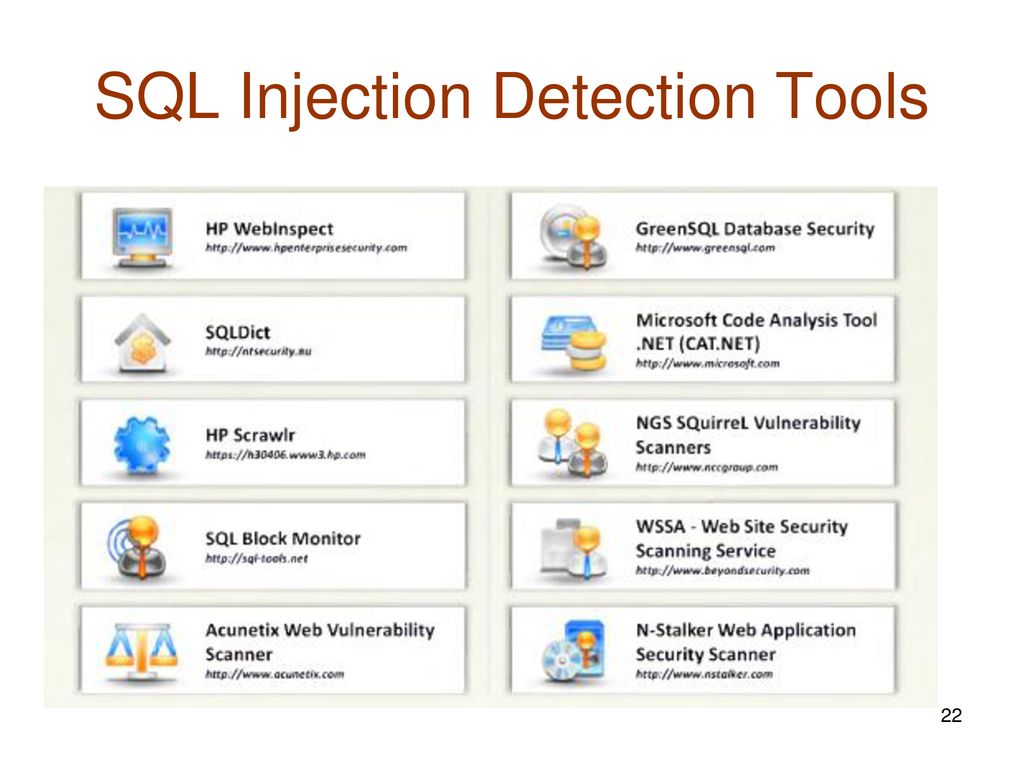
PDF] Comparing SQL Injection Detection Tools Using Attack Injection: An Experimental Study | Semantic Scholar
![PDF] Comparison of SQL Injection Detection and Prevention Tools based on Attack Type and Deployment Requirements | Semantic Scholar PDF] Comparison of SQL Injection Detection and Prevention Tools based on Attack Type and Deployment Requirements | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a7e46de3d021076f01e62cdd839e20be9192f287/4-Table1-1.png)
![PDF] SQL Injection detection using machine learning | Semantic Scholar PDF] SQL Injection detection using machine learning | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/04f57005444ca5c066df57887da1b2147e681e52/3-Figure1-1.png)